-
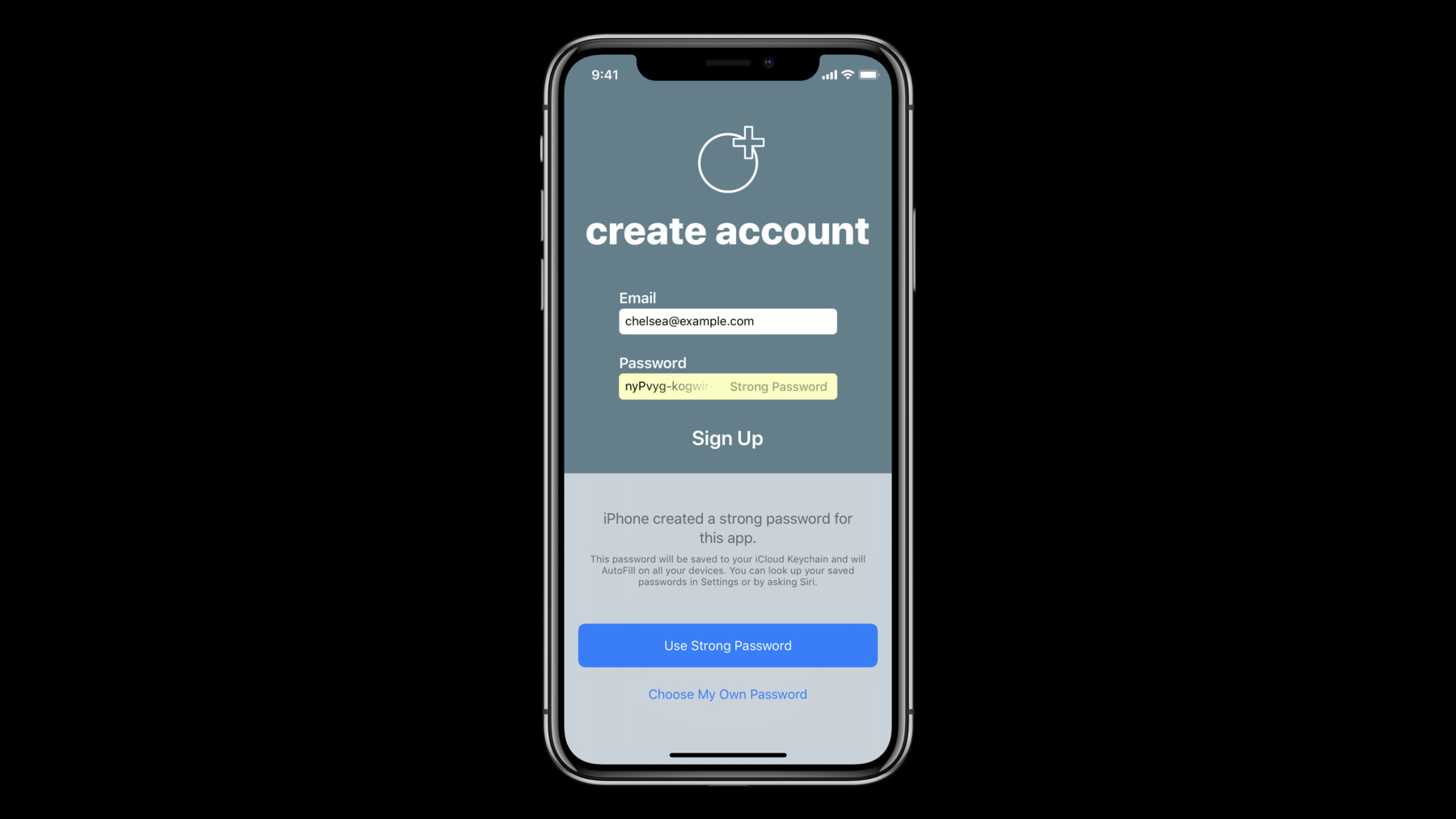
Automatic Strong Passwords and Security Code AutoFill
Passwords and security codes are a modern necessity required for security and privacy. iOS 12 eases the tedious aspects of account setup and sign-in by automatically suggesting and using strong, unique passwords — even from within apps — and by bringing one-time codes to the QuickType bar so users can fill them with one tap. Learn how to optimize your app to ensure that password, security code, and other AutoFill features provide a seamless way for your users to be more secure.
Resources
Related Videos
WWDC21
WWDC18
-
Search this video…
-